Scaling DevSecOps practices across product teams is critical but difficult to achieve. Software engineering leaders leading platform teams should integrate pertinent security tools as part of internal developer platforms to deliver secure software at scale.
See Gartner research for a sample listing of tools – Cool Vendors in Platform Engineering for Scaling Application Security Practices and How to Select DevSecOps Tools for Secure Software Delivery.
A platform approach to supporting DevSecOps workflows reduces the potential attack surface while still enabling development teams to deliver at scale.
Instead of having individual product teams implement security tools and practices at their own discretion, platform teams must provide “secure paved roads.” This ensures consistency and reduces the cognitive load of implementing security controls. The idea is to make the secure path the default path to production.
There are two prerequisite actions to making the secure path, the default path:
First, secure the software supply chain
Second, adopt a platform approach to application security
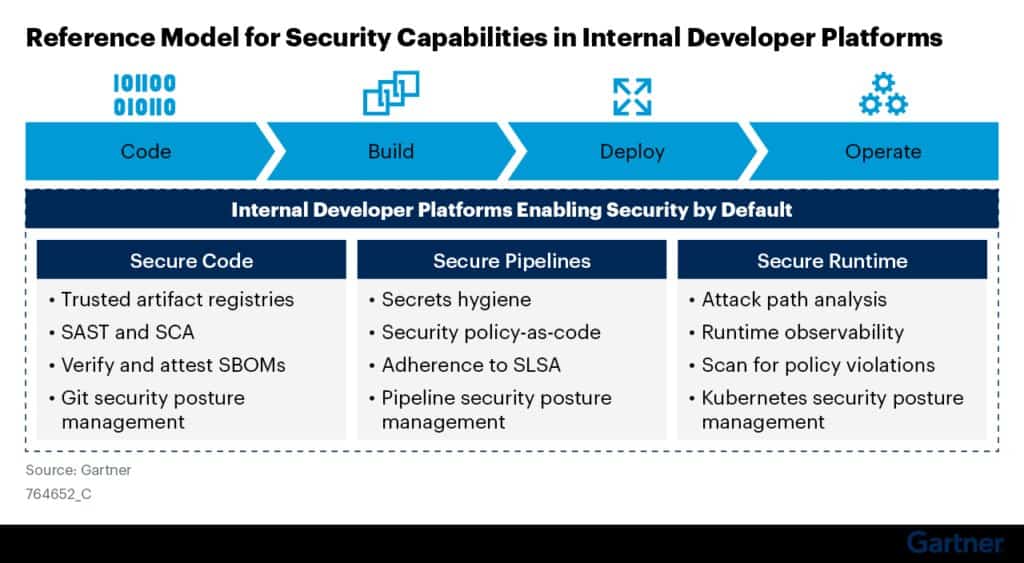
See Figure 1 for a reference model that shows how security capabilities can be integrated with IDPs.
Figure 1
Why integrate security tools as part of IDPs
Supply-chain levels for software artefacts, or SLSA (pronounced “salsa”) is a security framework – a checklist of standards and controls to prevent tampering, improve integrity, and secure packages and infrastructure.
One of the guiding principles of SLSA is to minimise the number of trusted platforms used for software development and execution. This is because platforms expand the attack surface for software supply chain attacks. Therefore, minimising the number of platforms decreases the attack surface.
As we saw in the case of SolarWinds, software development pipelines can be a prime target for supply chain attacks. Hardening platforms so they can be trusted involves significant effort and expensive manual work. Therefore, concentrating trust in fewer tools and platforms reduces cost, effort and risk. This is why we recommend IDPs and also integrating security workflows as part of IDPs.
Concentrate trust in shared infrastructure. For example, instead of each team within an organisation maintaining their own build platform, use a shared build platform.
– Source: Guiding Principles, SLSA
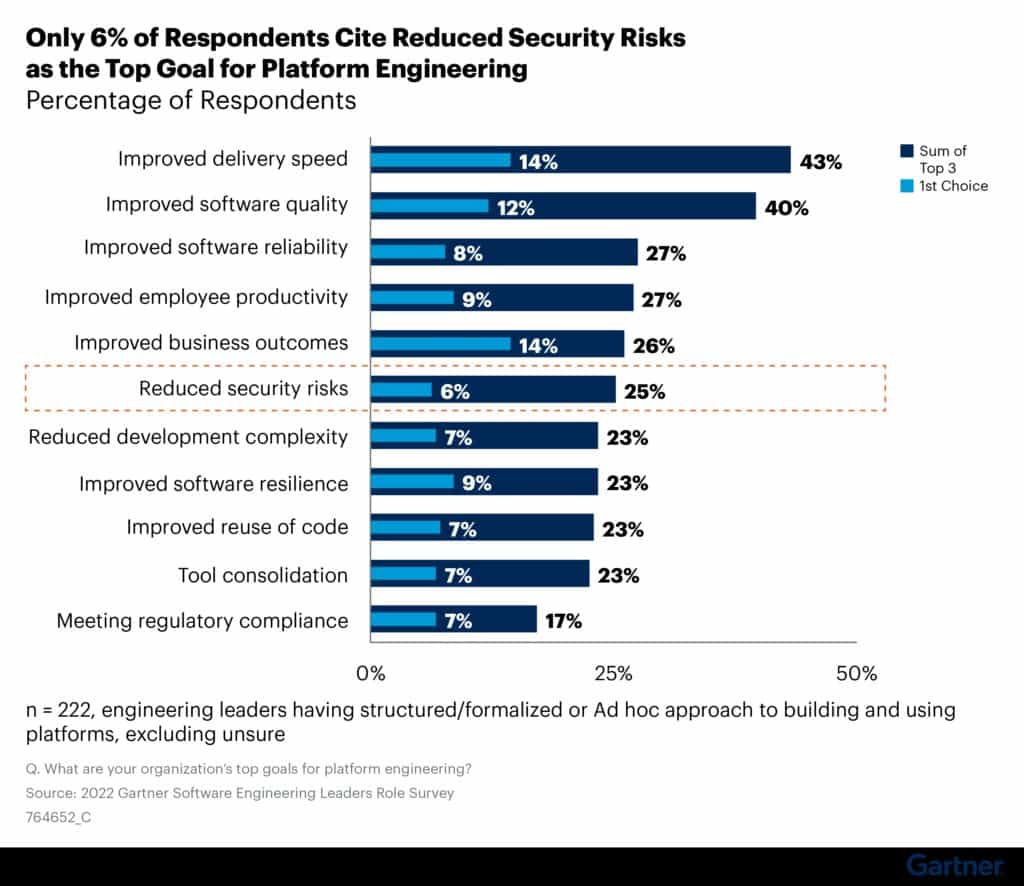
Gartner survey data reveals a missed opportunity
Platform teams focus on improving developer experience, developer productivity, software quality and delivery speed. According to Gartner’s 2022 Software Engineering Leaders Role Survey, only 25% of respondents cited “reduced security risks’’ as one of the top three goals for platform engineering and only 6% ranked it as the topmost goal. See Figure 2.
Using platform engineering to scale application security practices across the organisation is often an underappreciated and missed opportunity.
Figure 2
First published on Gartner Blog Network















