Statista predicts that public cloud services in Asia-Pacific will climb to US$15.8 billion by 2020 from 7.1 billion in 2015.
Naveen Chhabra, senior analyst with Forrester, says software as a service (SaaS) as one of the largest drivers for this trend. But Forrester cautions that the Asia-Pacific region are not sufficiently mature to support cloud solutions.
Ovum says the growing complexity of the cloud will require organisations to come up a more holistic management capability – including, and not limited to, the security aspects of the cloud.
During a series of C-suite roundtables in Southeast Asia conducted by CXOCIETY, we asked delegates to identify their biggest concern when it comes to moving business-critical applications to the cloud. Not surprisingly 57% of delegates, with business, finance and operational responsibilities, cited security as their number one concern.
Of the CIOs we’ve polled in these roundtables, all agree that security in the cloud is a given, particularly when outsourcing to cloud providers. Where the disagreement lies is the extent of accountability that both parties, service provider and customer, take in the security of the data.
As data moves between cloud, on-premise data centres, edge compute servers and consumer mobile devices, how does an enterprise design and deploy a security strategy that covers an expanding ecosystem of providers and customers while staying compliant to evolving regulations?

Alvin Rodrigues, Forcepoint’s senior director and security strategist for Asia-Pacific
FutureCIO spoke to Alvin Rodrigues (photo right), Forcepoint’s senior director and security strategist for Asia-Pacific, to discuss this perception as well as other trends driving and impacting adoption of security strategies among businesses in the region.
Rodrigues made it clear that cloud service providers (CSPs) have a shared responsibility. However, he conceded that regardless of the extent of such responsibility, the enterprise customer remains accountability to its customers, business partners and the regulator – regardless of the nature of the attack.
He commented that CSPs are under a lot of pressure to deliver the services at the lowest possible cost. The small ones will go for the bare minimum while those with reputations to maintain may go for the more higher-end solutions.
“There’s a fine line in between that because at some point, they will still cut off and there’s an accountability whereby data and people access are not on the onus of the cloud provider. You as an organisation generate the data, curates the data, loads the data onto the cloud and then manages the data. That’s still your responsibility, same goes for the application, that’s still your responsibility,” he countered.
Rodrigues noted that as much as 43% of corporate data is now in the cloud. Fifty-three percent of that is not necessarily controlled by IT. On average a company will have between 200 to 1000 cloud applications.
“When you consider the number of tablets, handphones and even PCs that are accessing applications and data in the cloud. If you consider that service providers are also accessing some of those applications as well as consumers, the cloud has become the new attack vector,” surmised Rodrigues.
In this environment how do you manage security. At this point traditional security measures and mindsets might not work. A rethink is in order. Rodrigues opined that everyone be reminded that the cloud is a shared responsibility.
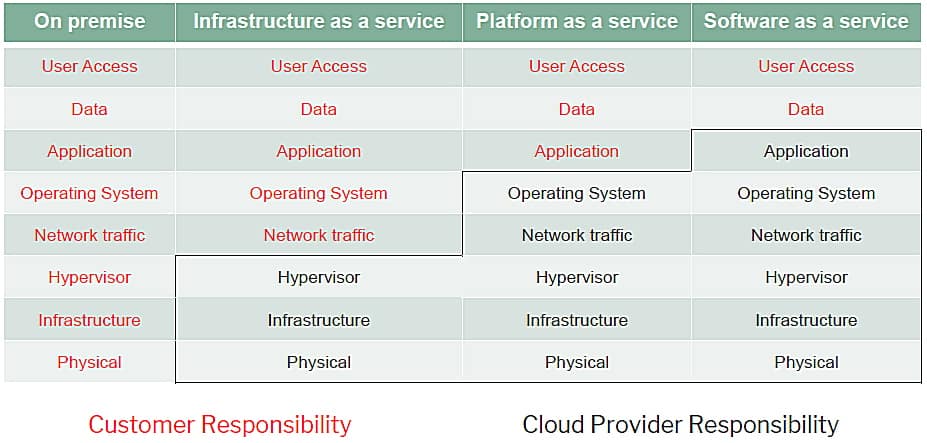
Figure 1: Security in the cloud – shared responsibility model
Source: Forcepoint
“In an on-prem environment, the entire responsibility is yours! When you have infrastructure as a service, you don’t look at the infrastructure but at your operating systems, your applications that are accessing the data. In platform as a service, you are responsible for deploying your application and your data onto this environment, and you use that as a platform monitoring,” he added.
In a software-as-a-service, responsibility still belongs to the enterprise, regardless what the vendor says. Rodrigues cautioned that when a breach occurs, everyone may share responsibility for the occurrence, but it is the enterprise customer that will face the brunt of the scrutiny.
Rodrigues conceded that regulators, business partners and end customers will not care which vendor and technology an enterprise takes towards securing infrastructure [on prem and in the cloud], application and data.
“The thing that binds CSPs and vendors is the Service Level Agreement. SLA is about uptime, availability, prevention of disruption, etc. Complicating the security challenge for the enterprise is the prevalence of shadow IT – technology the business units acquired without the support of the CIO and his or her team. Regardless however enterprise IT is still responsible for securing the environment,” he added.
Rodrigues acknowledged that cybersecurity, for example, is a convoluted discussion.
“At the end of the day, companies need to focus on building comprehensive cloud protection. Understand all the threats that are present in unsanctioned applications – including shadow IT – determine the risk level of the different apps, be able to identify and manage access rights of risky users. For sanctioned applications, it’s about managing unified policies so you can use the unified policy to enforce and prevent data leakage,” concluded Rodrigues.