
Study points to the prevalence of software supply chains in cloud-native apps
The Enterprise Strategy Group report, Walking the Line: GitOps and Shift Left Security: Scalable, Developer-centric Supply Chain Security Solutions, shows

The Enterprise Strategy Group report, Walking the Line: GitOps and Shift Left Security: Scalable, Developer-centric Supply Chain Security Solutions, shows

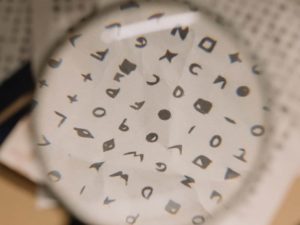
Whether for personal use or accessing your corporate network, authentication and authorisation are two critical concepts in access control. At

Merriam-Webster defines identity as “the qualities, beliefs, etc., that make a particular person or group different from others.” These qualities

The new security products allow companies to view their organisation as an attacker would.

Just as how other industries have adopted the ‘as-a-service model’, illicit service providers have done the same by selling tools,

Risk mitigation strategies all security engineers should know Enterprises that rely on dated software vendor patching models still find themselves

The city of Sapporo on the island of Hokkaido has deployed Nutanix Cloud Clusters (NC2) on AWS and selected Nutanix
Strong encryption is critical to protecting sensitive business and personal data. Google estimates that 95% of its internet traffic uses

With revenue of approximately US$364 million in 2021, Omdia predicts revenue from the Extended Detection and Response (XDR) market segment

Identity theft has become one of the most frequent tactics hackers use to achieve their malicious goals. Phishing personal information

The ongoing complexity of IT systems, along with evolving regulations are the major challenges faced by IT security professionals. IDC

Gartner forecasts worldwide IT spending to total $4.5 trillion in 2022, up three per cent from 2021. Overall IT spending