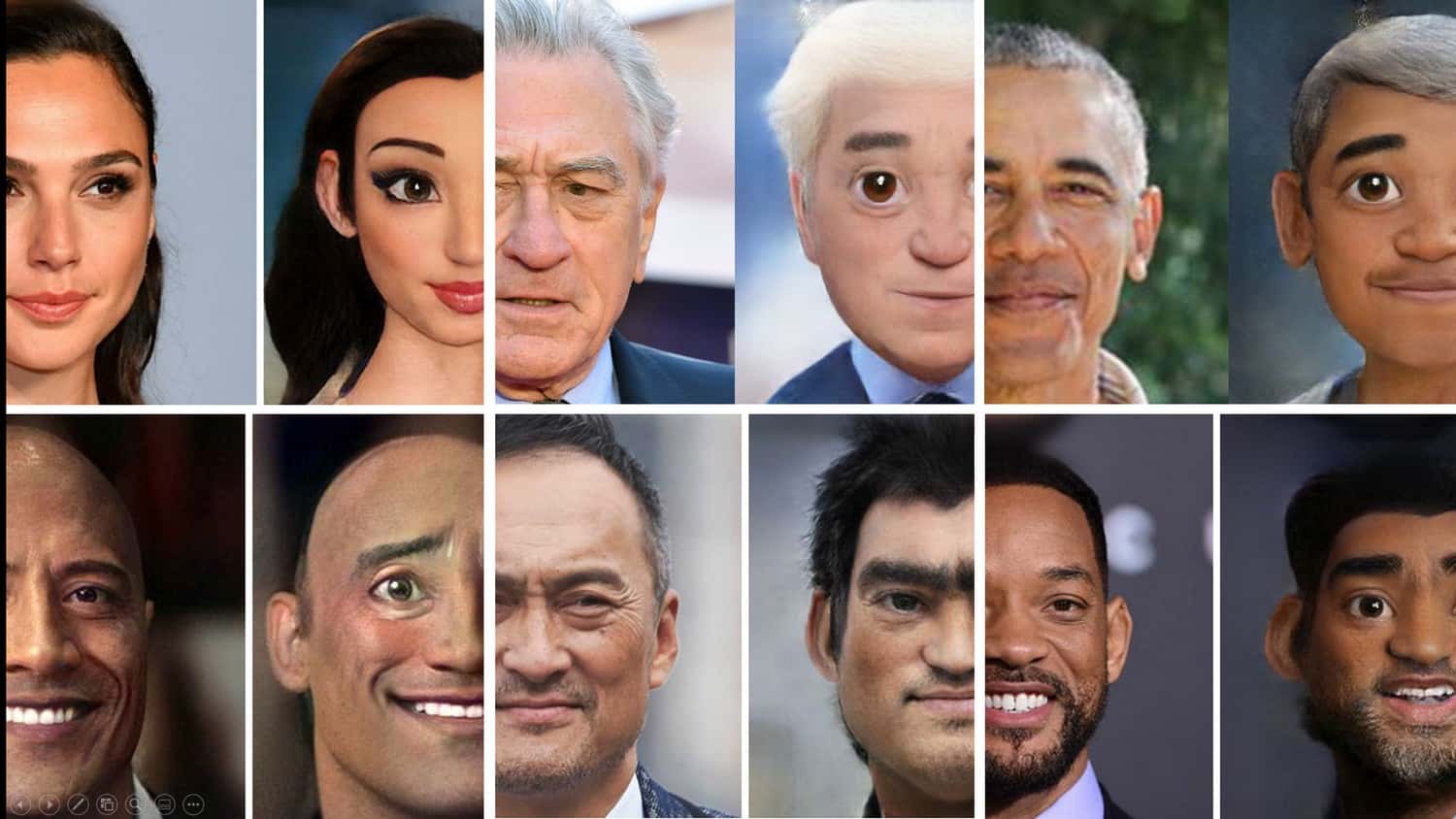
It’s the new thing on social media. Users are cartooning themselves, aka face photos. Check Point Research (CPR) raises some concerns particularly about how one app, Voila, because it includes specific and unique installation ID (vdid) can potentially be used by criminal elements.
Following a preliminary scan on the Viola app, CPR posted the following notes:
- The app has been written by a legitimate LLP company registered in the United Kingdom (UK)
- In terms of permissions, the app utilises only the bare minimum required for operation.
- The app verifies that the images contain face(s), and only after that verification, the app sends them to the server for processing
- All communication with the server is performed using HTTPS, so the traffic is encrypted out-of-the-box
- The app is using well known open-source libraries, where possible
- When the photo is sent to the server, the app includes the specific and unique installation id (vdid) that was generated by Google Play, potentially linking faces to the specific installation
Yaniv Balmas, head of Cyber Research at Check Point Software Technologies, commented that most users likely assume that the processing of Voila app is done locally on their phone. This is not the case. A non-obvious fact here is that the company sends face pictures to its servers for processing.
“When a face photo is sent to the company’s server, the app includes unique installation IDs that were generated by Google Play. Each photo is packaged up with user identification details. While this fact is mentioned in the company’s privacy policy, the possibility for misuse of the data opens up – either by the company itself or by a 3rd party,” he added.
He postulated that in the event of a hacked, the attackers could potentially gather a large data base of all faces of application users.
“We have no way of telling if the company is doing anything illegal or malicious, but I do think it’s important for new users to be aware of the inherent risks in sending content to servers for processing,” he continued.