Some years back, there was a flurry of activities by health regulators in Asia to digitally connect local healthcare systems – both public and private – to provide greater visibility of the health conditions of the populace.
The idea is if everyone in the healthcare system is connected, a doctor will be able to access the medical records and history of a patient and provide superior diagnosis and course of action. That is the ideal situation.
Unfortunately, cybercriminals also see value in the other information about a patient that is stored in health records. Hence, the data breach suffered by the Singapore Health Services (SingHealth) in 2018 that saw the non-medical data of 1.5 million records.
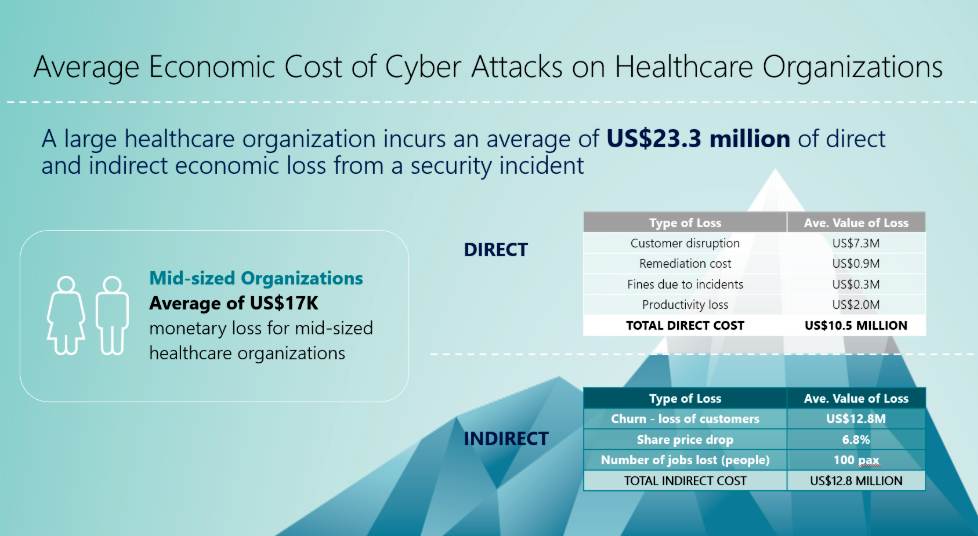
According to the CyberMDX report, Clinical Connectivity: Just the facts, medical information and health research data can be purchased for as much as US$1,000 per record.
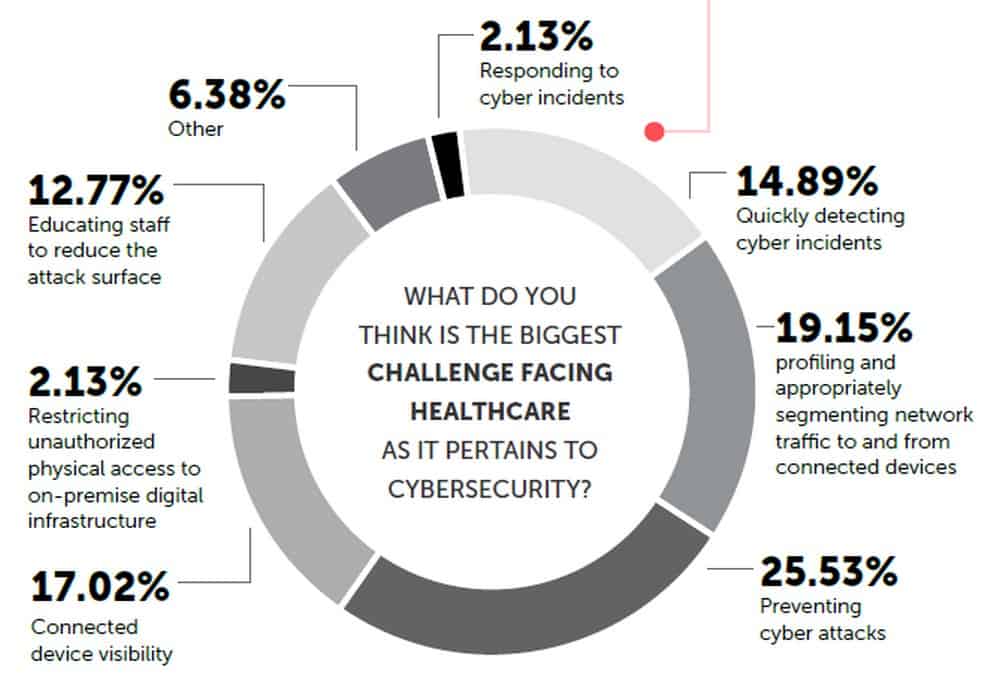
Source: CyberMDX 2020

Tony Jarvis, chief technology officer, Asia Pacific at Check Point Software Technologies noted that this valuable data can be used to obtain expensive medical services and prescription medications, as well as to fraudulently acquire government health benefits.
But beyond the data stored by healthcare providers, clinics and hospital authorities, there are also other areas of vulnerabilities that are just as lethal, possibly not well understood, or intentionally ignored, as in the case of a recent revelation by technology companies.
A new report from researchers at CyberMDX revealed that 22% of all Windows devices in a typical hospital are vulnerable to BlueKeep – a vulnerability in Microsoft’s Remote Desktop Protocol (RDP) services. First reported in May 2019, the bug allows for remote code execution.
The Bluekeep bug affects all unpatched Windows 2000 through Windows Server 2008 R2 and Windows 7. This was aggravated later on with the discovery of DejaBlue which affects newer Windows versions including Windows 10 and its predecessors. Unfortunately, it doesn’t stop there as Metaspoilt exploit was discovered to have been released into the public in September 2019.
Just to be clear, many of the smart devices that hospitals are using today, including X-ray machines, medical scanners, and even smart hospital beds are built on software sitting atop an operating system.
Researchers at CyberMDX disclosed in January 2020 that seven GE Healthcare devices that monitor patient vital signs can be taken over by a hacker once it is able to enter a hospital’s network. The exploit can highjack the telemetry aggregation servers and prevent the monitors from issuing alerts, putting patient lives at risk.
The affected GE devices include:
- Central Information Center (CIC), versions 4.x and 5.x
- CARESCAPE Central Station (CSCS), versions 1.x and 2.x
- CARESCAPE Telemetry Server, versions 4.3, 4.2 and prior
- Apex Pro Telemetry Server/Tower, versions 4.2 and earlier
- B450 patient monitor, version 2.x
- B650 patient monitor, versions 1.x and 2.x
- B850 patient monitor, versions 1.x and 2.x
Unfortunately for hospitals using these equipment, patches won’t be available until sometime in Q2 2020 (according to a story published on ZDNET).
In November 2019, GE Healthcare issued an Urgent Medical Device Correction but its recommendation was to ensure that the vulnerable devices are connected to a network separate from the rest of the hospital network. Arguable this is a band aid solution. When you consider that as many as 10-15 connected medical devices per bed (US hospital), such a recommendation while understandable is not the best solution.
According to Check Point’s Jarvis the inherent vulnerabilities associated with healthcare devices, such as a lack of encryption of sensitive data as well as hard-coded or default login credentials, prevent IT professionals from even implementing security patches, should such patches even exist.
He concedes that the benefits that connected medical devices offer cannot be ignored. They supply patients and healthcare providers with potentially life-saving information and enable an efficient way of handling this data. He cautioned however healthcare organisations must be aware of potential vulnerabilities and do their best to mitigate any perceived risks.
“Network segmentation is a best practice which would allow IT professionals in the healthcare sector to embrace new digital medical solutions while segregating them from other critical systems, thereby reducing the risk of vulnerabilities spreading throughout the organisation,” he concluded.
When you consider that as many as 450 million connected healthcare assets globally, who should take ownership for the safety of patients’ health and their privacy?
Given that many of the smart medical devices being used today earn their manufacturers millions, shouldn’t they be held accountable?
Source: Understanding the Cybersecurity Threat Landscape in Asia Pacific: Securing the Modern Enterprise in a Digital World, Frost & Sullivan 2018















