While it is still early days before we can predict a post-coronavirus Asia, the global pandemic has proven to be the biggest test of how modern and flexible working practices can enable employees to stay productive, working anytime, anywhere on any device.
Today’s enterprise mobility technologies allow employees to remotely connect to the data and resources they need, whenever they need them and on whatever devices they choose. As countries including Singapore take steps to extend full or partial lockdowns and mandate social distancing in both professional and leisure gatherings, remote working has become an organizational business continuity measure to be widely applied, rather than a workplace culture to appeal to the millennia workforce.
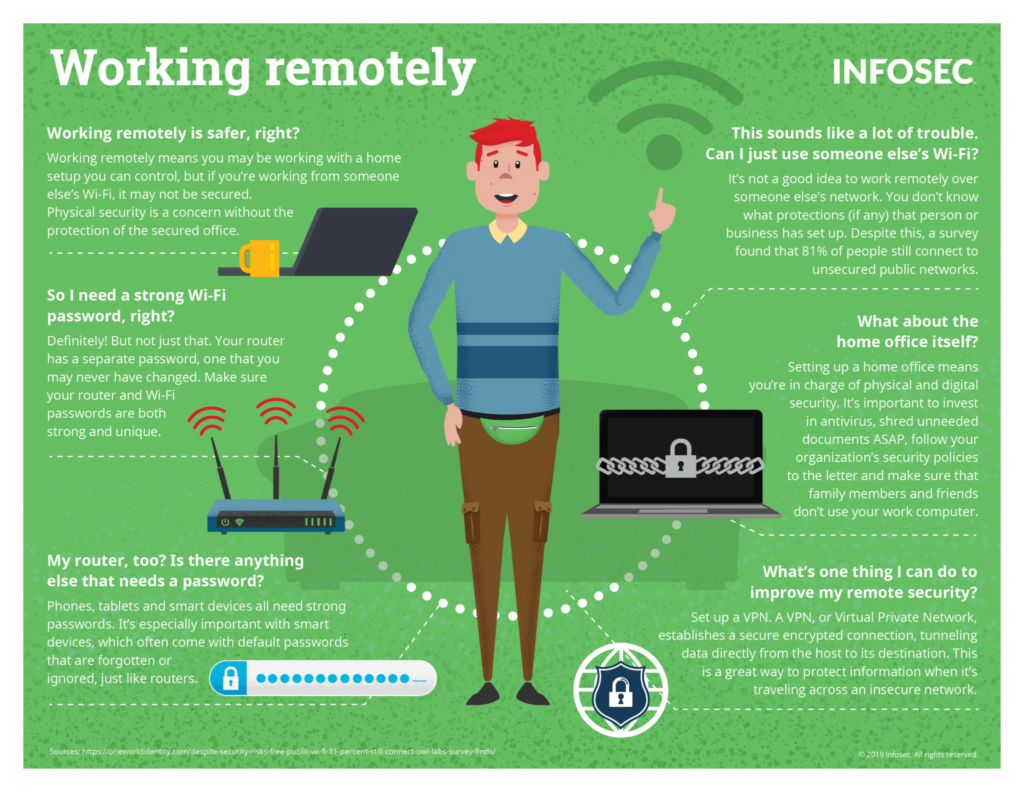
Yet remote access to organizational data and systems, via various mobile devices across multiple networks, has a dark side that keeps chief information security officers (CISOs) awake at night. Accessing data outside the secure network perimeter opens unprecedented “attack surfaces” for cyber criminals and creates a huge amount of additional vulnerability for organizations.
What are the risks that CISOs and IT decision-makers need to look out for when they deploy remote working practices, and how can they be mitigated?
Capacity issues
Mobile workers use virtual private networks (VPNs) to access corporate networks, but VPNs put considerable strain on resources, as organizations need to ensure enough licenses are available for secure remote access.
Additionally, IT decision makers need to consider who gets priority bandwidth within their secure access solutions. One common problem happens when users try to upload or download large files that are non-business critical, which exhaust the bandwidth dedicated to the operation of critical corporate IT systems.
During business continuity and disaster recovery planning, organizations should carefully consider capacity factors, including licensing and bandwidth availability to accommodate any unexpected surge in demand.
To securely allocate web traffic to cloud applications, IT decision-makers should consider using Cloud Access Security Broker (CASB) solutions to manage the demands, while maintaining security monitoring and security policies to ensure that users and applications are properly protected.
Enterprises may also wish to leverage the security functions available to them through the existing services that they already consume, such as Microsoft Azure, as some of these may help to quickly alleviate challenges.
Unsecured devices
Patches and updates address known security problems, which means that ignoring them opens new attack vectors for cyber criminals. IT decision-makers need to implement proper patching processes to maintain enterprise-wide security, especially in bring your own device (BYOD) scenarios, where native mobile device security software might not live up to organizational standards.
This requires visibility of what is connecting to the network, a view into the state of health of those devices and when they were last updated, as well as visibility of new hardware and software updates and ensuring they are applied promptly.
Suspicious behaviour becomes difficult to monitor
As remote working takes place outside the confines of the corporate security perimeter, it disrupts the baseline working patterns that enterprise threat analysts need to look for. If logging in at 11pm is an option, then security analysts need to be aware of this pattern “as a new normal” when analysing suspicious behaviour.
This will allow them to reset the baseline of normal access behaviour, instead of flagging remote access that’s outside of the “old normal” as suspicious.
Instead of restricting employee flexible working patterns, organizations can consider ways to monitor behaviours that can compensate for unusual but legitimate remote access situations. User and Entity Behaviour Analytics (UEBA) tools, provide enhanced visibility and reporting of user behaviour, while delivering the contextual awareness that threat analysts require to establish whether a given behaviour is suspicious, freeing up time and resources to deal with real threats quickly and effectively.
Attackers exploit mobile device usage behaviour
The danger of users responding to phishing emails on a mobile device is becoming an increasing concern, as Google noted that it saw more than 18 million daily malware and phishing emails related to COVID-19 scams alone in a week of April 2020.
This is possibly due to the limited device screen size, which makes it harder to spot tell-tale warning signs of a phishing email, or behavioural attitudes where users tend to use mobile devices on-the-go to check and respond to emails.
As most mobile users have multiple email accounts on one device, any oversight of phishing attacks on personal email accounts can adversely impact organizational networks when the enterprise device gets compromised.
Phishing and smishing (phishing via SMS) attacks also tend to exploit users’ trust of native and commercial social networking apps. As the pandemic situation evolves, there is a rise of cyber campaigns through SMS and consumer apps, like WhatsApp, that exploit the fears of users who are anxious for more information.
Since the risk lies primarily with the people using mobile devices, rigorous education around mobile device usage policies, with clear guidelines on the acceptable use of consumer applications and personal email accounts on corporate and BYOD resources, is recommended.
Physical device breaches
Mobile devices for work are at risk of being lost, stolen or compromised. Devices left unattended in public spaces, even with strong encryption and protection, present a direct and significant security risk to enterprise data, both on the device itself and on organizational networks further afield.
As with protection against phishing, when it comes to physical device safety and security, mobile device users need to be educated on company policies and the responsibilities that come with using devices that have access to critical corporate data.
Devices with strong device encryption methods provide some protection against being compromised or jailbroken, while remote device management capabilities can automatically remediate with a remote lock, device or enterprise wipe or other quarantine controls.
Malicious Apps
As our personal and professional lives converge on mobile devices, users will inevitably download apps for personal use on corporate-owned devices, potentially exposing these devices to spyware and security vulnerabilities that can be exploited to access corporate data and systems.
Mobile device usage policies need to outline the acceptable terms of use to prevent data loss with app sharing permissions, app-level password enforcement and if required, application whitelisting and blacklisting. Security teams should also routinely monitor devices to search for known malicious applications, and direct users to delete them immediately.
Enabling remote access to corporate resources while safeguarding the integrity of organizational systems remains a tough yet necessary balancing act to implement technology with trust and responsibility in mind.
By leveraging the intelligent mobility management tools, analytics and insights that are available today, enterprise IT and security teams are now better equipped to provide their work colleagues with a secure remote access model, where the employee mobile working experience is optimized, productivity is maintained and the strain on organizational IT resources is contained.