The 2020 Hong Kong Encryption Trends Study by the Ponemon Institute concluded that the “new work-from-home normal” following the COVID-19 pandemic has accelerated digital initiatives among Hong Kong enterprises.
The report suggested that this brings even more attention to data protection and encryption strategies, with protection of customer information their number one priority. However, many organizations face challenges deploying encryption technology.
The report noted that enterprise encryption adoption rate in the city is among the highest in the world with 60% of Hong Kong companies surveyed revealing they have a consistent plan or strategy, compared to the 48% global average.
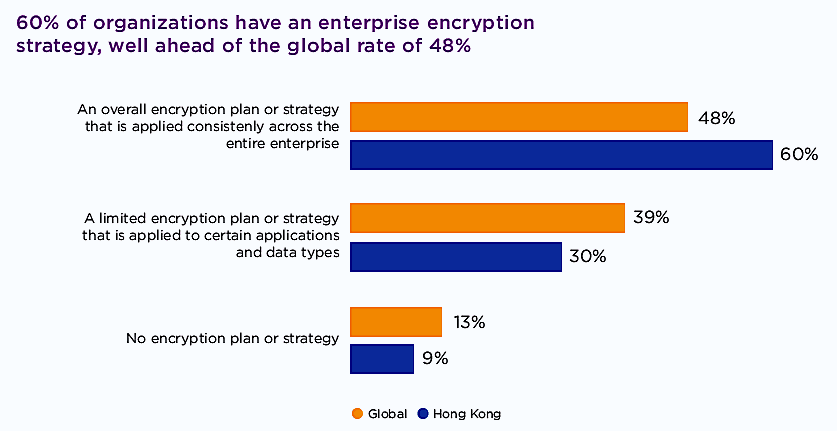

Speaking to FutureCIO, Ian Christofis, principal managing consultant at nCipher Security, acknowledged that the very strong uptake in encryption also means continued decline in organisations that don’t have an encryption strategy, with only 13% and 9% of survey respondents globally and Hong Kong as not having an encryption strategy.
Despite the growth in encryption uptake, there remains critical challenges with 57% of Hong Kong companies saying that initially deploying the encryption technology is the biggest challenge in planning and executing a data encryption strategy.
In addition, 49% say that discovering where sensitive data resides in the organization is a top challenge – the lowest rate across regions surveyed.
Christofis commented that “IT people in organizations are always much happier to have the data encrypted and not have to fend off any false accusations that they did something wrong. They would much rather that they can do their job without being falsely accused of touching data that they shouldn’t have control over.”
He concluded that IT people are big supporters of having the data encrypted. “Which means then your access control can happen at a separate level to that of the IT-based hierarchy and access control,” he added.
Hardware vs Software
The software-is-everything story is an over-arching argument of the digital economy. But when it comes to data encryption there are those who believe that hardware offers better data protection.
According to Christofis protecting things purely with software means introducing limits to that protection. He suggested that most security problems are from software. He cited the example of OpenSSL software with the Heartbleed attack. In this case, the fault was only discovered two years after the bug was introduced to the software.
“If you are relying on software-only to protect your data, ultimately that level of assurance is quite low. To get strong cryptographic protection, you should have hardware at least to protect the master key so that if everything is turned off and things are in the storage and things are not running actively then everything is protected. Because if you have data and you encrypt it under a key – Where do you put that key?
“Rather than effectively leaving the key under the doormat, if I encrypt the key under another key, and maybe encrypt that key under another key. You can keep doing that, but ultimately that top-level master key has to be somewhere. The best place for that [master key] is to be protected by a hardware security device, like a hardware security module (HSM),” he continued.
It should be noted that nCipher sells HSM.
Christofis said the hardware security device is designed effectively to be a bit like a teller behind the screen of the bank, you can ask the hardware security device like the teller to do things on your behalf, but you don’t just get to reach behind to get the cash from the drawer yourself.
“That’s sort of the difference you’ve got, you got the separate device that only does certain things, it won’t ever give you the cryptographic key. It will just use those cryptographic keys when you give it specific, properly authorized instructions to do so,” he elaborated.
“So, what it does for you is protect the cryptographic keys and their usage to only authorized systems. Ultimately, if you have cryptographic solutions, if you don’t use hardware security then you really haven’t got very strong security because you have effectively left those keys under the doormat.”
According to Christofis hardware or cryptographic security is common. For example, every mobile phone has a lot of specific hardware security devices in the phone. They call it Secure Element, Secure Enclave, or in laptops the TPM chip, etc., or it could be a smartcard. The essence of hardware protection is the same, it is a separate device that will protect the cryptographic keys and only do certain things.
The use of hardware security devices to protect cryptography has grown enormously, particularly with the use of mobile phone. Mobile phones are very sophisticated in their use of cryptographic protocols and hardware security protection, etc. All of that is done in a user-friendly seamless way, so it’s all ‘under the covers’ so people don’t realize it is there.
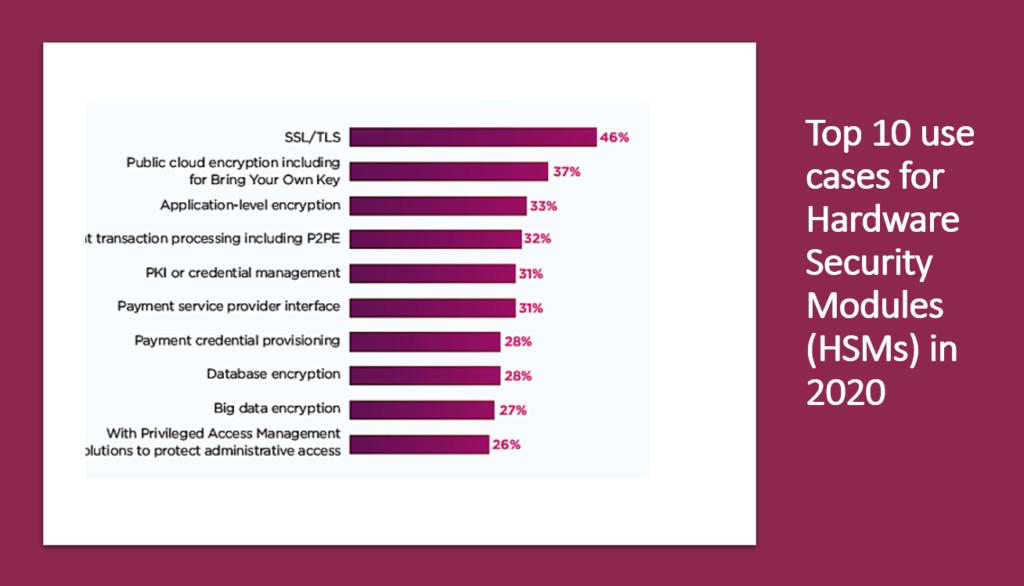
But having encryption hardware on devices needs to be properly matched at the server side. He confided that HSM can be found in the data centre performing encryption at very high speed in high volume to protect at least the top-level keys and maybe lower level keys as well, depending on the architecture.
“As attacks have been happening, the use of that hardware is seen as increasingly important. Even if you use the security facilities of the public Cloud vendors themselves, they use hardware security modules (HSM) to protect the services that they offer,” he added.














