
SGX 200 companies do not actively block email fraud
Proofpoint says 59% of SGX 200 companies do not have the necessary email authentication protocols in place, leaving their customers,

Proofpoint says 59% of SGX 200 companies do not have the necessary email authentication protocols in place, leaving their customers,

* Editor’s note: This article is co-produced by Sukhpreet Kaur For years, information security has been floating in the Top 10

Driven by the growing demand for endpoint security platforms, identity and access management software and managed security services, the total

Cybersecurity investment is broken Cybersecurity is now the #1 spend item on the technology investment list. In 2022, 88% of

The LexisNexis Risk Solutions Cybercrime Report revealed that the second half of 2021 showed a significant shift to mobile fraud

Cloud-based authentication service provider, Okta, is the latest tech company to experience a breach of their systems. Ransomware group Lapsus$

The ongoing conflict in Ukraine has posed a grave danger to lives and businesses and will have profound consequences extending
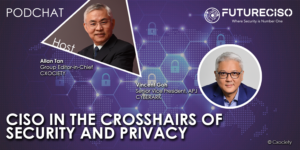
The CISO is responsible for the vision, strategy, and program to ensure the protection of information assets, and technologies. As

IT decision-makers are complacent about risks to the business from phishing and BEC (Business Email Compromise – also known as

The global transformation of banking and payments has only accelerated over the past few years, and between web trends and

The Frost & Sullivan report, Global Surveillance Solutions Growth Opportunities, finds that the increasing adoption of advanced surveillance systems and

That businesses in Asia-Pacific are adopting cloud computing technology is no longer being debated. The journey to the cloud, whether