The lead story from HackerOne is that US$100 million paid to white hackers globally, 25% of whom are based in Asia-Pacific.
The story suggests that there is a potentially lucrative career opportunity on the good side of hacking, or they call it bug bounty.
A bug bounty is a monetary award given to a hacker who finds and reports a valid security weakness to an organisation so it can be safely resolved.
Technically, it is a win-win for both sides. Bug bounty hackers, and the organisations they affiliate themselves with including HackerOne, gain both a reputation for their skills while being paid for it. For enterprises, it is a chance to get bugs identified and hopefully fixed before more malicious hackers discover these and wreak multi-faceted havoc on the business.
“We started out as a couple of hackers in the Netherlands with a crazy belief that hackers like us could make organisations safer and do it more efficiently and cost-effectively than traditional approaches,” explained HackerOne co-founders Jobert Abma and Michiel Prins in their blog post about the milestone. “US$100 Million in bounties later, maybe this idea isn’t so crazy after all. Thank you to all the hackers who have made the internet safer one vulnerability at a time. Hacking is here for good, for the good of all of us.”
The success rate in finding flaws or bugs in software programming can suggest either of two things: original codes is not being as thorough as they should be. Without suggesting a lack of care in software development it also reveals a potential pressure faced by the programming community – the requirement to turn things around as quickly as possible to facilitate what business leaders refer to as “faster time-to-market”.
The result is sometimes overlooked as coding errors. As someone who used to write code for a living, I can attest that it is easy to not see what an errant code can lead to, particularly when viewed from the bigger picture. I say this because we have started to promote the concept of microservices – small codes that do one job.
But I am straying here.
HackerOne CEO Marten Mickos said the goal is to build a community able to test and vet every piece of the “digital connected civilisation”.
“US$100 Million is a number that attracts the best hackers, providing companies and governments unmatched ROI, significantly reducing the risk of data breach. We have arrived at the point in history where you are ignorant and negligent if you do not have a way to receive useful input from ethical hackers. In this new world of ever-evolving threats, the only way to get ahead is to get transparent. Openness, not secrecy, is the way forward,” he adds.
The positive power of a growing community of ethical hacker pools industries’ defences against data breaches, reduces cybercrime, protects privacy, and restores trust in the digital society.
And this may well be a trend to see, programmers at enterprises will continue to develop code based on the requirements of the lines of business, with oversight from IT to ensure compliance to stated governance policies. A best practice would then mean invoking the aide of ethical hackers who will do a code review hopefully before the application is released into production.
This easy-way-out route has the potential for organisations to ignore implementing more stringent vulnerability and patch management programmes. Which will reveal themselves in more breaches down the line? Vendors use disclaimers and lengthy end-user license agreements (EULA) to get away from the responsibility of going beyond doing their best to ensure that software is clean when the end-user installs the software into his or her device.
This should not be tolerated by governments, regulatory bodies and by the industry.
Vendors make a lot of money from the software – embedded or out-of-the-box – they sell. They should be mandated to use a sizeable chunk of their revenue and profits to clean their code.
The same goes for industries including banks and retailers who in their haste to create the next wunderapp ignore the rules and best practice of software coding.
Trending
- 84: The number of new hackers that sign up to the platform every hour
- US$6,000: The amount of bounties paid out on the platform every hour
- 214%: Year-over-year hacker-powered security growth in the federal government
- 85.6%: The year over year growth in total bounty payments, with a 17.5% increase since February when COVID-19 was declared a pandemic.
- 343%: The increase in signups over the past year on Hacker101 — HackerOne’s free online classes for aspiring hackers.
- 38%: The increase in average weekly new registrants for Hacker101 since February, when COVID-19 was declared a pandemic.
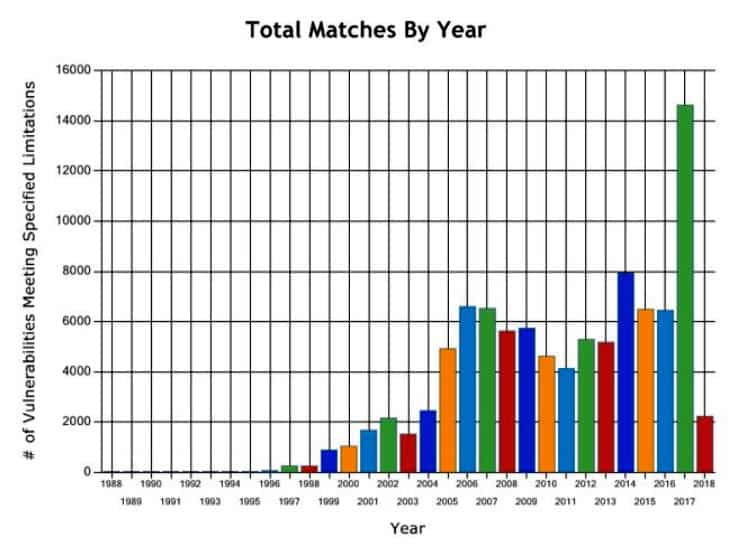
- Over 170,000: The number of vulnerabilities hackers have uncovered in nearly 2,000 customer programs