According to the Identity Theft Resource Center, there were 878 cyberattacks in 2020, 18% of which were recorded as ransomware.
Key findings
According to Unit 42’s 2021 Ransomware Threat Report, the average ransom payment nearly tripled, and the highest ransom payment and demand each doubled in 2020.The average ransom paid for organisations increased from US$115,123 in 2019 to US$312,493 in 2020, a 171% year-over-year increase. Additionally, the highest ransom paid by an organisation doubled from 2019 to 2020, from US$5 million to US$10 million. Meanwhile, cybercriminals are getting greedy. From 2015 to 2019, the highest ransomware demand was US$15 million. In 2020, the highest ransomware demand grew to US$30 million.
For instance, Maze ransom demands in 2020 averaged US$4.8 million, a significant increase compared to the average of US$847,344 across all ransomware families in 2020. Cybercriminals know they can make money with ransomware and are continuing to get bolder with their demands.
Healthcare organizations as targets
Ransomware operators took advantage of the pandemic to prey on healthcare organisations, arguably the most targeted vertical for ransomware in 2020.
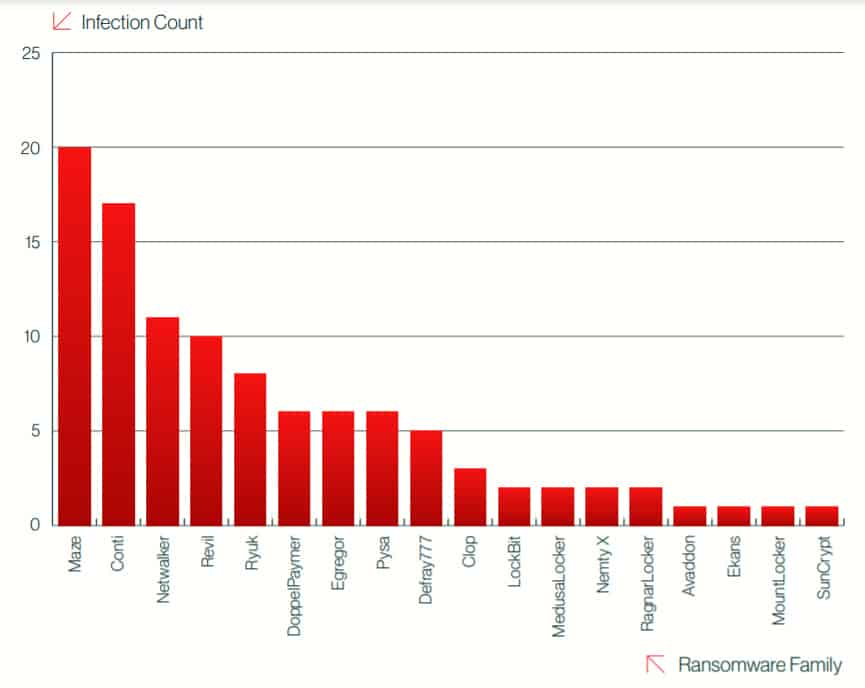
Ryuk ransomware stood out from the pack. In CrowdStrike’s 2021 Global Threat Report Ryuk is fifth from the top common ransomware attacks against the healthcare sector behind Maze, Conti, Netwalker and Nevil.
Double extortion
A typical ransomware attack involves encrypting data and forcing the victim to pay a ransom to unlock it. Double extortion extends the attack by leaking the stolen data on leak sites on the dark web. Netwalker is infamous for this form of attack.
Tomorrow’s ransomware
Hackers are continually looking for organisations to target and they know that ransomware is not only effective, but can also be low-effort, especially if using the Ransomware-as-a-Service model. It is expected more and more operators will follow this path.
At least 16 different ransomware variants are now threatening to expose data or utilizing leak sites and more variants will likely continue this double extortion trend. The use of anonymized service will also continue to grow, which makes it more difficult for security researchers and law enforcement to track.
Recommendations
Defending against ransomware attacks is much like protecting against other malware, albeit carrying a much higher risk to the organisation.
Initial Access
Initial access is relatively consistent across all ransomware variants. Organisations should maintain user awareness and training for email security as well as consider ways to identify and remediate malicious email as soon as it enters an employee’s mailbox. Organisations should also ensure they conduct proper patch management and review which services may be exposed to the internet. Remote desktop services should be correctly configured and secured, using the principle of least privilege wherever possible, with a policy in place to detect patterns associated with brute-force attacks.
Backup and recovery process
Organisations should continue to back up their data and keep an appropriate recovery process in place. Ransomware operators will target on-site backups for encryption, so organisations should ensure that all backups are maintained securely offline.
Recovery processes must be implemented and rehearsed with critical stakeholders to minimize downtime and cost to the organisation in the event of a ransomware attack.
Security controls
The most effective forms of protection from ransomware are endpoint security, URL filtering or web protection, advanced threat prevention (unknown threats/sandboxing), and anti-phishing solutions deployed to all enterprise environments and devices.
While these will not outright guarantee prevention, they will drastically reduce the risk of infection from common variants and provide stopgap measures, allowing one technology to offer a line of enforcement when another may not be effective.