Cybersecurity commissioner stresses the importance of teamwork at (ISC)² Conference
In cultivating talents in the field of cyber security (ISC)², a non-profit association of certified cybersecurity professionals, today introduced a new entry-level certification in Asia Pacific.
According to a Cybersecurity Workforce Study by the non-profit, the global cybersecurity workforce has a shortage of 2.72 million professionals. Asia Pacific has the largest regional gap – 1.42 million cybersecurity professionals are needed to fill the demand.
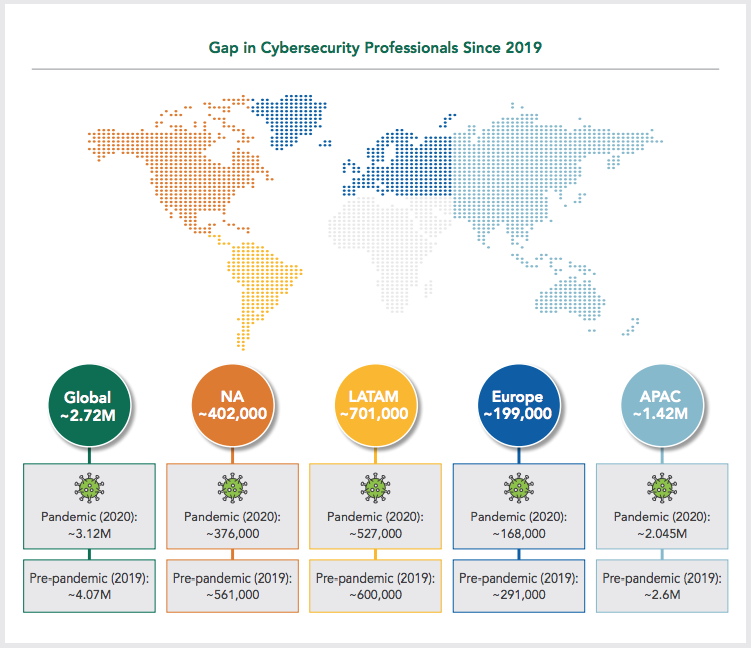
Image source: https://www.isc2.org//-/media/ISC2/Research/2021/ISC2-Cybersecurity-Workforce-Study-2021.ashx
The certification is offered as a pilot programme for individuals without prior cybersecurity experience. The certification is developed to nurture a new generation of cybersecurity professionals into the field, irrespective of age, industry, or skill levels.
Opened to university graduates to mid-career professionals, the certification will assure employers that the candidates have the foundational knowledge, skills and abilities to enter the job market at junior levels.
In removing language barriers, the English certification will be translated into Chinese, Japanese, and Korean for candidates in the region to smoothen the transition for new entrants into the sector in the future.
IT and OT convergence brings new vulnerabilities
Few of the best minds in cyber security gathered at the (ISC)² SECURE event recently, to learn about the developments in cyber security threats, share new ideas and refine best practices.
Speaking at the conference on the convergence of IT and operational technology or OT, David Koh, the commissioner of cybersecurity and chief executive of Cyber Security Agency of Singapore, believes that cybersecurity to be a team sport. Since the cybersecurity landscape is constantly evolving, the stakes remain high for any enterprise, large or small.

The convergence of OT and IT, operational technology systems has unlocked new OT functions and capabilities, making things more efficient, such as remote monitoring.
With this, operations and even logistics, power plants, manufacturing operations, aeroplanes, trains, now send data back and forth to the manufacturers and they receive updates through remote access connections.
Besides these efficiencies, all this shift has come at a cost. The attack surface from a cybersecurity perspective for operational technology has vastly widened the range of IT cybersecurity threats.
- David Koh
Image source: FutureCIO"Professionals with different types of expertise need to work together to build a tight-knit community. It is particularly important to this profession. Teamwork drives successful outcomes and we need to work together to better defend our cyberspace."
David Koh, CSA chief executive and commissioner of cybersecurity
What used to be a safe OT environment before has now changed because cyber attacks can now affect OT systems. The risks posed can spill over to the physical world and have real-world impact, including potentially life-threatening consequences. The convergence of IT and OT is just one example of how cybersecurity is constantly evolving.
Cybersecurity is a team sport
No one single entity, organisation or even the government holds all the levers to combat cyber crimes. Government tech agencies, private sector companies, and professional associations like (ISC)², all need to work together in order to deal with this looming threat.
CSA updated its national cybersecurity strategy to highlight one of the key shifts to recognise cybersecurity talent as a foundational enabler, to underpin all of its strategic pillars.
The commissioner said that each organisation in turn, contributes to a picture at the sectoral level, and ultimately gets merged, in any organisation, at a national picture.
“The success of a good defence strategy hinges on people and talent. We have our job to do and it is important for each of us to know what role we play, and how they contribute to the larger picture at the organisational level.” said Koh.
His analogy of a team sport, posits that professionals are the main players who are defending organisations, their network, digital assets and their clients.
Defending against a cyber attack can come down to the single person on duty for that day, who notices something and shares the information, which then goes to the sector out of the gate, and on to the national picture.
This is then shared with other organisations who may not have noticed that incident as well. This is why it is important to develop talent, their keen instincts, so that each player can professionally and play their part. regardless of where he is.





