One of the Philippines’ real-life heroes, Jose Rizal, is quoted as saying: “He who does not know how to look back at where he came from will never get to his destination.”
I am sure he wasn’t thinking about cybersecurity, but it may be just as valid. Perhaps by recognising what went wrong in 2021, enterprises can be better prepared and adept at countering the cyber threats coming our way in 2022.
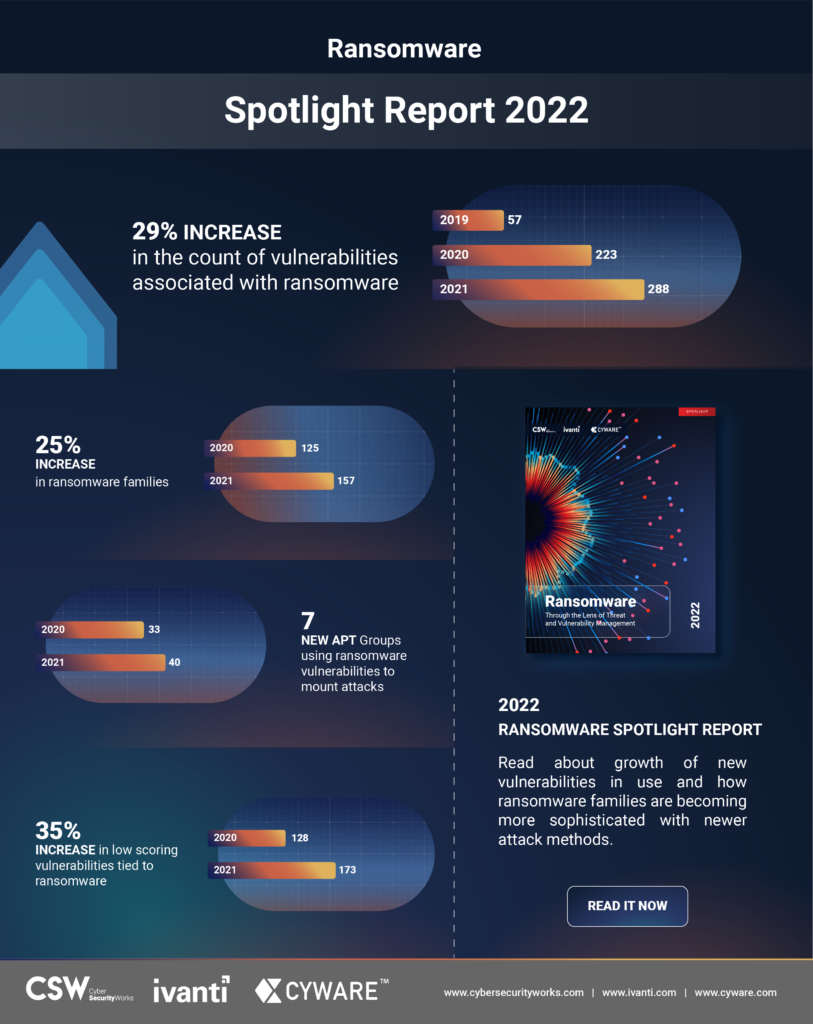
Ivanti’s Ransomware Spotlight Year End Report revealed a 26% increase in the number of ransomware families now circulating among us.
Source: Ivanti
Some observations
Unpatched vulnerabilities – the most prominent attack vectors
The analysis uncovered 65 new vulnerabilities tied to ransomware last year, representing a 29% growth compared to the previous year and bringing the total number of vulnerabilities associated with ransomware to 288.
About 37% of these newly added vulnerabilities were actively trending on the dark web and repeatedly exploited.
In parallel, 56% of the 223 older vulnerabilities identified prior to 2021 continued to be actively exploited by ransomware groups.
This proves that organisations need to prioritise and patch the weaponised vulnerabilities that ransomware groups are targeting – whether they are newly identified vulnerabilities or older vulnerabilities.

According to Srinivas Mukkamala, senior vice president of security products at Ivanti, ransomware groups are becoming more sophisticated and their attacks more impactful.
These threat actors are increasingly leveraging automated tool kits to exploit vulnerabilities and penetrate deeper into compromised networks. They are also expanding their targets and waging more attacks on critical sectors, disrupting daily lives and causing unprecedented damage. “Organisations need to be extra vigilant and patch weaponised vulnerabilities without delays. This requires leveraging a combination of risk-based vulnerability prioritisation and automated patch intelligence to identify and prioritise vulnerability weaknesses and then accelerate remediation,” he added.
Heavily leverage zero-day vulnerabilities
Ransomware groups continue to find and leverage zero-day vulnerabilities, even before the CVEs are added to the National Vulnerability Database and patches are released.
The QNAP (CVE-2021-28799), Sonic Wall (CVE-2021-20016), Kaseya (CVE-2021-30116) and most recently Apache Log4j (CVE-2021-44228) vulnerabilities were exploited even before they made it to the National Vulnerability Database (NVD).

This dangerous trend highlights the need for agility from vendors in disclosing vulnerabilities and releasing patches based on priority. It also highlights the need for organisations to look beyond the NVD and keep an eye out for vulnerability trends, exploitation instances, vendor advisories and alerts from security agencies while prioritising the vulnerabilities to patch.
Anuj Goel, CEO at Cyware says the substantive change we’ve observed across the ransomware landscape is that the attackers are looking to penetrate processes like patch deployment as much as they look for gaps in protection to penetrate systems.
Vulnerability discovery must be met with an action that treats vulnerability data as intelligence to drive swift response decisions. As ransomware gangs operationalise their tooling, methods, and target lists, it is essential for SecOps teams to automate processes to self-heal vulnerable assets and systems to mitigate risk through real-time intelligence operationalisation,” he continued.
Supply chains are favourite targets
Ransomware groups are increasingly targeting supply chain networks to inflict major damage and cause widespread chaos.
A single supply chain compromise can open multiple avenues for threat actors to hijack complete system distributions across hundreds of victim networks. Last year, threat actors compromised supply chain networks via third-party applications, vendor-specific products, and open-source libraries.

For example, the REvil group went after CVE-2021-30116 in the Kaseya VSA remote management service, launching a malicious update package that compromised all customers using onsite and remote versions of the VSA platform.
According to Aaron Sandeen, CEO of Cyber Security Works, ransomware is devastating to customers and employees in every sector.
He predicts that in 2022, “we will continue to see an increase in new vulnerabilities, exploit types, APT groups, ransomware families, CWE categories and how old vulnerabilities are leveraged to exploit organisations. Leaders need innovative and predictive help to prioritise and remediate ransomware threats.”
Cyberthreat as a service up for sale
Ransomware groups are increasingly sharing their services with others, much like legitimate SaaS offerings.
Ransomware-as-a-service is a business model in which ransomware developers offer their services, variants, kits or code to other malicious actors in return for payment.
Exploit-as-a-service solutions allow threat actors to rent zero-day exploits from developers.
Dropper-as-a-service allows newbie threat actors to distribute malware through programmes that, when run, can execute a malicious payload onto a victim’s computer.
Trojan-as-a-service, also called malware-as-a-service, enables anyone with an internet connection to obtain and deploy customised malware in the cloud, with zero installation.
With 157 ransomware families exploiting 288 vulnerabilities, ransomware groups are poised to wage rampant attacks in the coming years.
Coveware says organisations pay an average of $220,298 and suffer 23 days of downtime following a ransomware attack. This calls for an increased emphasis on cyber hygiene. Looking ahead, automating cyber hygiene will become increasingly important, especially as environments continue to get more complicated.





