Have you ever noticed that when one security vendor issues an alert, a slew of others appears very quickly after that? It’s like there is no other news to tell, no other warning to issue. It’s also futile to read multiple security reports because the observations will likely be the same, the report is the same, and the solutions are almost always the same. Well, the same depends on the vendor reporting – because changes are, the recommendations will be based around what they offer.
But that’s just me.
I did have the opportunity to meet with Sharat Sinha, vice president and GM for Asia Pacific at Check Point Software Technologies, and among the issues we discussed was the content of the 2020 Cyber Security Report (CSR), but more what the Check Point Research (CPR) is predicting that is different this 2020.
To be clear, the interview was done before the World Health Organisation categorised the coronavirus outbreak in Wuhan, China as COVID-19 so the global panic has not yet started – at least not in Bangkok where I met with Sinha.
Describe the cyber threat landscape across Asia Pacific today
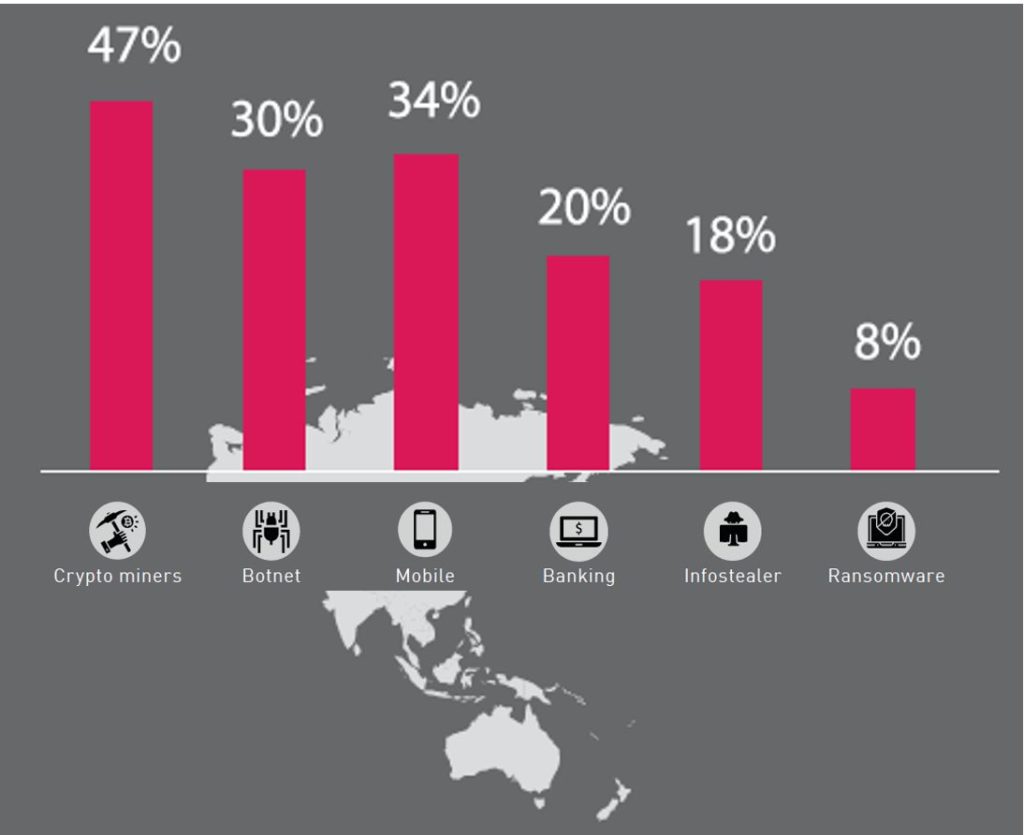
Source: 2020 Cyber Security Report, Check Point Software Technologies
Sharat Sinha: One would be vectors. We observed that cloud, mobile, and IoT are the 3 primary vectors. If you look at the nature of cyberattacks, ransomware has been big in the last 12 months, but these keep changing, that’s the current trend.
Another key trend is that hackers now are very well funded. We are seeing very well structured cyberattacks implying plenty of preparation on the part of hackers. Cybercrime, as a business, is a very well-structured.
Enterprises must likewise build a well-structure countermeasure, ideally preventive in nature.
Why are organisations vulnerable to hacking and breaches? How should they approach security?
Sharat Sinha: Enterprises should take a prevention-based approach. The idea is to prevent a breach before it happens. Because once you are breached, the only recourse is remediation. So, again prevention-based approach is the best course of action.
Second, enterprises should look at a consolidated architecture across their cloud, mobile, data centre, network, IoT – the entire infrastructure.
Once you take these two approaches, your probability of getting hacked becomes extremely low.
What is your advice to CISOs and CIOs to help them secure the budget they need to protect the enterprise?
Sharat Sinha: CISOs and CIOs should look at a comprehensive infrastructure. This should cover everything that they have – from application, infrastructure, number of users that are going to use it, and then take an approach to consolidate it. So that they can have a broader budget for the organisation.
They should also take a preventive-based approach. When you take prevention-based approach through a consolidated architecture, typically the total cost of ownership goes down. Operationally it becomes much easier, including a decrease in operating cost. The requirement of the cost related aspects themselves go down, and it becomes much easier to justify to the board and the finance organisations.
Given the prevailing shortage in security professionals, what are the options for enterprises?
Sharat Sinha: There are a couple of options. A comprehensive approach to security architecture allows an enterprise to have optimum number of resources.
For example, a typical enterprise might have 20+ specialists in cybersecurity. You employ specialists for specific technologies, and because large enterprises operate in siloes, it means getting multiple people trained for each technology. If you take a consolidated approach, you could be anywhere from 1 — 4 technologies being used, and in such cases, the number of resource requirements goes down.
You can also look at a combination of insourcing and outsourcing to get the right balance of skills.
The choice of insourcing or outsourcing depends on the level of threats, because even if you choose to look outside the organisation, the outsource agency may be able to provide people with god technology skills but you still need to get the right capabilities [something that may be unique to the business].
Right capability depends on whether you have the right resources for handling it, whether you had a comprehensive view on the whole architecture, whether you have considered all aspects of access to your enterprise, internally or externally.
What is a proactive approach to cybersecurity?
Sharat Sinha: In order to have a proactive approach to cybersecurity, an enterprise should look at consolidated architecture, with a centralised management, which will have oversight over the entire infrastructure. When combined with a prevention-based approach, this minimises remediation costs and helps you keep the operations team lean but well trained.
Throughout the discussion Sinha reiterated the importance of prevention as the best form of cyber defence. It reminded me of two rather old isms: forewarned is forearmed, meaning having knowledge of the possible dangers or problems gives us a tactical advantage. Of course, only if we do something with the knowledge.
The other is an ounce of prevention is worth a pound of cure. In the cyber security context, preventing an attack by providing a solid defence structure is preferable to going through what is almost always an expensive, time consuming remediation process that entails discovering what happened, recovering what was stolen and rebuilding lost confidence.