Securing privileged access has never been an easy task for organizations. With several high-profile breaches linked to breach of privileged credentials, security teams are now increasingly aware of the high risk associated with these privileged accounts.
The recent SolarWinds attack only further validates the need to secure these privileged accounts. Once the defence of an enterprise has been breached, the privileged accounts become the primary target of attackers.
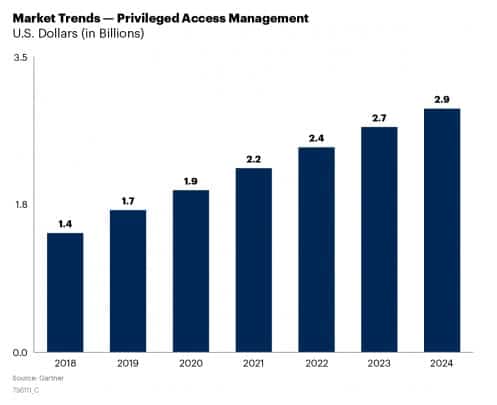
All these factors along with accelerated migration to cloud, blurring enterprise security perimeters and the sheer increase in the number of cyberattacks, are all contributing to the growth of Privileged Access Management.
Trending and Competitive LandscaPPE
PAM will continue to witness increased interest and adoption among enterprises of all sizes in near future. To cash in on this growing interest, PAM providers need to re-evaluate how they are strategically positioned in the market.
The competition in the PAM market remains intense with a multitude of players. First there are large global enterprises such as CyberArk, BeyondTrust, Thycotic and Broadcom and then there are regional players such as ARCON in EMEA and Asia/Pacific, senhasegura in Latin America (LATAM), and WALLIX in Europe which leverage their local expertise to gain an edge in particular region.
The vendors primarily strive to compete basis the strength of their technical capabilities and ability to address emerging use cases. The large enterprises which had embraced PAM solutions early on are now exploring advanced use cases such as securing credentials used by software and machines referred to as “secrets management” or providing elevated privileges for limited time called as “Just-in-Time” privileged access. They are curious to investigate how AI and machine learning capabilities could be leveraged in PAM use cases.
The focus of PAM implementations has also expanded from large enterprises to mid-size organizations and SMBs. Many of these are now implementing or exploring PAM programs. To target these first-time buyers, PAM providers will need to assess their value proposition and how it can be aligned with this resource sensitive segment – both in terms of skills as well as finance.
My latest research note Competitive Landscape: Privileged Access Management analyses the competitive landscape in this space and discusses the strategies PAM solution providers can adopt to differentiate in the market.
First published in Gartner Blog Network







