In 2020, threat actors focused their efforts on Covid-19-related threats, ranging from email threats, and business email compromise, to social engineering, and malware bundled in apps. Trend Micro estimates nearly nine million Covid-19-related threats were detected in the first half of 2020.
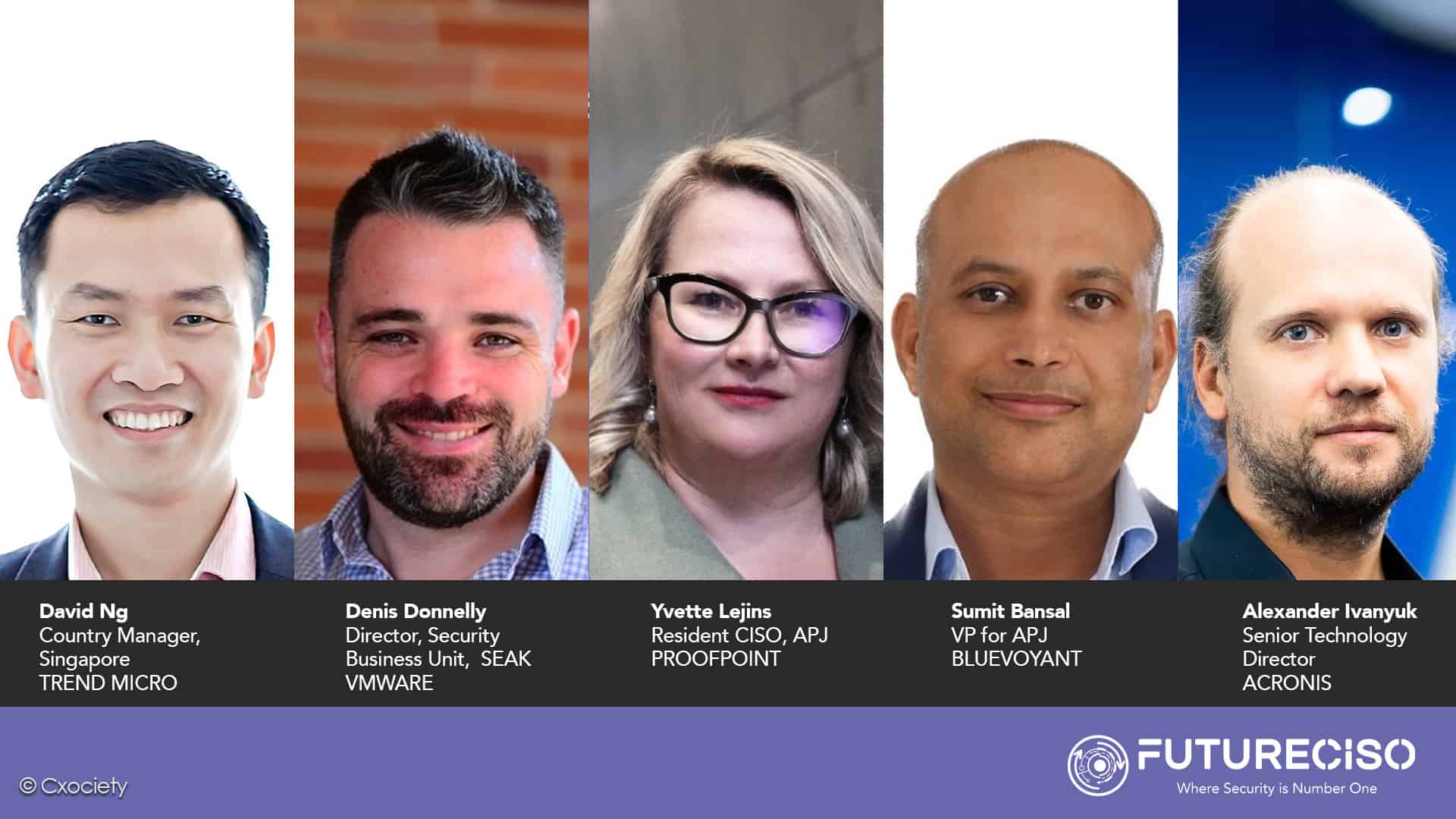
“Since then, we’ve seen a focus on two other areas. First, ransomware developers have continued their shift towards more lucrative monetization methods, such as ransomware-as-a-service, with detections increasing over the years. Second, there is a strong emergence of advanced persistent threat (APT) groups,” said David Ng, country manager, Singapore, Trend Micro.
Phishing has emerged as a major cyber threat in Asia Pacific (APAC). Proofpoint’s 2022 State of the Phish report found varying levels of occurrence and frequency across Australia and Japan. In Singapore, phishing scams have seen a significant increase in reported cases, and compromised credentials can lead to supply chain attacks.
Yvette Lejins, the resident CISO for APJ at Proofpoint, says insider threats have also risen, and hybrid work has made cybersecurity policies more critical. “Organisations must update their cybersecurity policies to prevent a loss of sensitive and critical data,” she added.
Why breaches happen
In 2021, companies spent US$2 billion on endpoint detection and response (EDR) solutions. By 2031, this will reach US$18 billion. But even with $2 billion being spent on security, companies big and small still get breached. Denis Donnelly, director for the security business unit with VMware SEAK, acknowledged that the EDR market is growing rapidly but that it’s just one piece of an end-to-end security architecture that companies need to put in place.
“It’s crucial that companies keep the people, processes, and technology triad in mind when evaluating and purchasing EDR solutions. They need to also ensure that their operational processes are kept up to date and they provide adequate training for all employees to mitigate security breaches,” he voiced out.

“There is no silver bullet in cyber defence,” argued Sumit Bansal, BlueVoyant vice president for APAC and Japan. He adds that attackers only need to be right once to gain unauthorised access to steal data, credentials, or personal information.
“Defenders need to be right all the time or to quickly spot an issue. While organisations are making strides with their cyber security, phishing, password reuse, and unpatched systems remain common attack vectors because they work.”
Sumit Bansal
The zero trust equation
Security proponents argue that introducing a zero trust framework in the security strategy may strengthen an organisation’s cyber defence capability.

Acronis’ senior technology director, Alexander Ivanyuk believed that the company will be better secured, possibly reaching the best possible level at this moment. “But that doesn’t mean that it is 100% secure and will never be breached,” he warned.
“Security is pretty similar to insurance – it can help in case something bad happens. The better insurance you get, the more coverage it provides. You will also tend to spend less money later because any security is much cheaper than the consequences of a breach and recovery.”
Alexander Ivanyuk
Lejins agreed to add that implementing a zero-trust approach and enhancing security strategies is a step forward, but the threat landscape is ever-evolving with new methods constantly continually being developed.
“As fast as cybersecurity firms can come up with solutions, it is critical that organisations implement cybersecurity awareness training programs to educate employees about the importance of their role in cyber defence,” opined Lejins
Reasonable cybersecurity budget in 2023
VMware’s Donnelly commented that despite the constant reminders for increased security, justifying a reasonable security budget is not as easy or straightforward. “It depends on your industry, the country of your HQ and how much sensitive data you process, amongst others,” he added.
The EU’s Agency for Cybersecurity’s (ENISA) report from last November, shows that security expenditure of the overall IT budget ranges from 5.8% in Sweden to 8% in Lithuania, and from 5.3% in the Energy sector to 9.6% in the Digital Infrastructure segment. A more globally focused report from Deloitte shows that financial institutions invest an average of 10.9%.
Ivanyuk from Acronis said a good gauge is around 10%. Half of the organisations allocated less than 10% (source) of their IT budget to security. “What’s important is that every company must have a cybersecurity budget that covers all vectors of attacks. The very bare minimum is to protect endpoints as they are being attacked the most, starting with backing up the data stored on these machines,” he continued.
BlueVoyant’s Bansal opined that a reasonable security budget varies by industry and organisation size. He suggested that organisations should look for continuous monitoring of internal and external threats, plus a layered approach. He also observed that especially for small to mid-sized businesses, outsourcing to vendors could be more cost-effective and provide economies of scale.

“Every organisation’s security budget will differ based on needs,” said Proofpoint’s Lejins.
“Instead of thinking about setting aside a percentage of dollars, companies need to understand their unique risk profile and determine the data that is important to them and their customers. It’s then about making sure programs and investments in technologies reduce these risks to acceptable levels”
Yvette Lejins
Futureproofed security strategy – the holy grail
Is it possible to futureproof a cybersecurity strategy? Given that technology is a moving target, perhaps one way to futureproof a cybersecurity strategy is to keep it moving with the times. Arguably the better goal is cyber resilience.

Ng said a holistic security strategy should focus on operationalizing cyber risk management across the enterprise. “This entails two key areas – first, the ability to proactively manage and reduce risk; second is greater visibility into attack surface risk,” he added.
“A combination of attack surface management, extended detection and response (XDR), and zero trust will help organisations gain better insights and control and proactively reduce risk exposure.”
David Ng
For Lejins, people and not technology are the most critical variable in today’s cyber threats. “Prioritising a human-centric zero-trust approach with a focus on security awareness training is necessary for organisations to encourage employees to take an active role in cyber defence. Investing in security infrastructure is not enough, the human factor needs to be made central to cybersecurity strategies,” she posited.
How do CISOs/CIOs balance the hype surrounding information security?
Bansal conceded that it can be hard for security teams to monitor and handle hundreds of alerts a day, plus make sure they are maximizing all their licenses and subscriptions. Combined with this is the shortage of skilled workers to fill the open roles in cyber security.
“CISOs/CIOs may want to consider vendors that take a platform approach and can provide multiple services. Or hire a managed security provider which can monitor multiple systems and help enterprises get the most from them,” he offered.
Lejins said it is more important to assess the approach according to the company’s risk profile, rather than buying a “generic” solution built into existing tools. “It’s like buying a multi-vitamin when you really need just Vitamin D tablets – while it will do some good, the overall investment may not be best,” she opined.

Donnelly agreed that CISOs and CIOs identify their gaps, and priorities and how to address these within the budgetary and personnel constraints.
“Given the current recession fears in many markets, and continued difficulties in finding skilled cybersecurity personnel, it would be prudent for CISO/CIO leaders to consolidate tools, and in turn vendors.”
Denis Donnelly